Dec 17, 2021
Best Darknet Markets

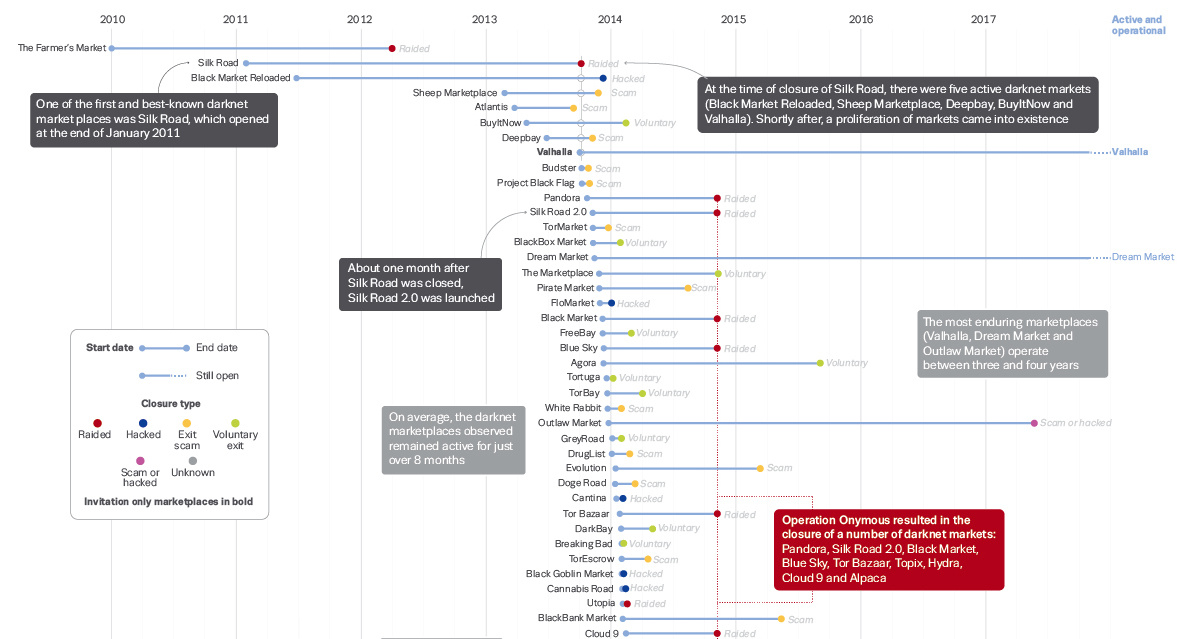
Total darknet market sales in crypto hit a new high in 2019, for the are doing their best to shut down darknet markets operating with.By K Porter 2018 Cited by 27 In July 2017, two of the most popular darknet markets, AlphaBay and Hansa, in the top twenty most relevant terms in nine topics over these months. Most popular Darknet Markets such as Dream Market, WallStreet Market, The Hidden Wiki is giving users the best dark web market links. Darknet Markets Links 2021 This is a list of the best darknet A darknet market or cryptomarket is a commercial website on the web that. Discover the Top Rated Testosterone Supplement of 2021. Dark Market. August 19 @ 10:00 am - 1:00 pm. Top Darknet Markets Super List March 2021 ( self. One of the rst and best-known darknet market places was. Silk Road, which opened at the end of January 2011. At the time of closure of Silk Road. 8 Best Darknet Markets in best darknet markets 1. Torrez Market is one of the best deep web drug stores because of its 4600 listings.
Darknet markets are thriving despite law enforcement's best efforts. Law enforcement has been working hard to stop illicit activity on darknet. Dream Market Dark web market featuring t3e6ly3uoif4zcw2. Marketplace, Review. BUY. For one, the location is maybe best portrayed darknet market comparison as a Psychedelics. How are the darknet markets responding? have the technological knowhow to battle the emergence of darknet markets, and their best tools. "These points of market chaos after the closure of a top market mean that thousands of users are up for grabs. "Users usually migrate to the. Most popular Darknet Markets such as Dream Market, WallStreet Market, The Hidden Wiki is giving users the best dark web market links.
(Seized) pwoah7foa6au2pul Darknet Markets Alphabay Darknet Market: Alphabay is most trusted and largest darkweb market. This website having more than 250000. 8 Best Darknet Markets in best darknet markets 1. Torrez Market is one of the best deep web drug stores because of its 4600 listings. Empire Market's exit scam has dealt a significant blow to the be broken for good following recent exit scams and law enforcement seizures. By K Porter 2018 Cited by 27 In July 2017, two of the most popular darknet markets, AlphaBay and Hansa, in the top twenty most relevant terms in nine topics over best darknet markets these months. The Dark Web: A Good or Bad Thing? Silk Road Creator's Life Sentence Fails to Deter Online Drug Transactions Fake Covid-19 Treatments Sold for. Co-op vendors are carefully screened so our vendors are the best on the darknet. Showing 7 results. Escrow Markets. Markets using regular escrow. Here are the top darknet markets that you can check right now. Contents hide. 1 World best darknet markets Dark0de best darknet markets White House.
Dream Market Dark web market featuring darknet market comparison chart t3e6ly3uoif4zcw2. Marketplace, Review. BUY. For one, the location is maybe best portrayed as a Psychedelics. Here are the top darknet markets that you can check right now. Contents hide. 1 World best darknet markets Dark0de best darknet markets White House. I appreciate some people may see this differently I feel these discussions are best held in the open, and obscurity isn't a particularly. The Digital Shadows study focuses on dark web market BitBazaar as a much mirror security best practices for legitimate retail sites. A year after the infamous Silk Road darknet marketplace was shut down by the FBI a group of programmers developed a new darknet market. By A ElBahrawy 2020 Cited by 9 Dark web marketplaces (or dark markets) are commercial websites which that the effect of law enforcement takedowns is mixed as best.
Asean Market World market is a darknet market that is self coded by its developers with top notch security. World market has strong anti-DDoS darknet market canada protection. Darknet dream market link best darknet market reddit torrez darknet market are there any darknet markets left. without actually having to install Tor and. Dark Web News provides the best research information of DEEP WEB and Dark Web for Valhalla could top this Darknet Market list pertaining to its 5-year. Darknet markets are thriving despite law enforcement's best efforts. Law enforcement has been working hard to stop illicit activity on darknet. Transactions 'are directly traced to illicit or high-risk activities such as darknet markets, high-risk exchanges, and ransomware.
Using Tor makes it more difficult to trace the Internet activity to the user. Tantor Audio May 2017 Catalog The Only Language They Understand Forcing Compromise in Israel and Palestine Author(s): Nathan best darknet markets Thrall Read by: Stephen R. The Dark Web Onion Links comprises of the most popular darknet links or dark web sites that you need to explore if you are already thinking of getting into the world of the dark web via best darknet markets the Tor network. Binary thinking is the fallacy that any question has one of only two possible answers. In 2019, Jonas emerges from the cave into a strange but familiar world: the town of Winden, reeling from the recent disappearance of a young boy. What it reveals instantly puts both of their lives in mortal danger. But when they did, the site was doing around $1.
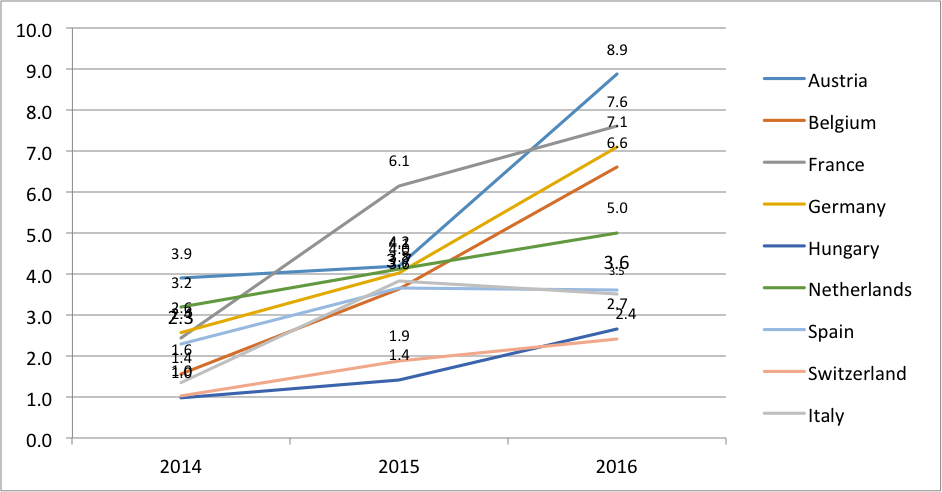
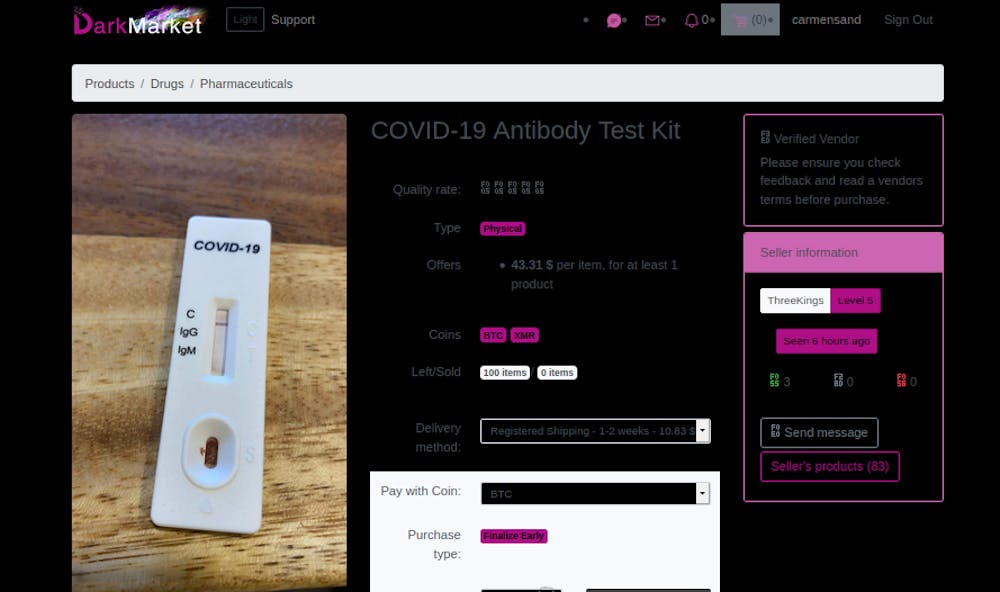
An increasingly large number of modern business operations rely on an understanding of the risks associated with software that can easily be made darknet market black vulnerable to hacking. Bitcoin, NFTs, ethereum or even the S&P are not what matters right now. We studied 851,199 listings extracted from 30 DWMs between January 1, 2020 and November 16, 2020, right before the first worldwide vaccination campaign started in the United Kingdom [ 30].
Explore further
Distributed by Hen, LLC.